March 2023
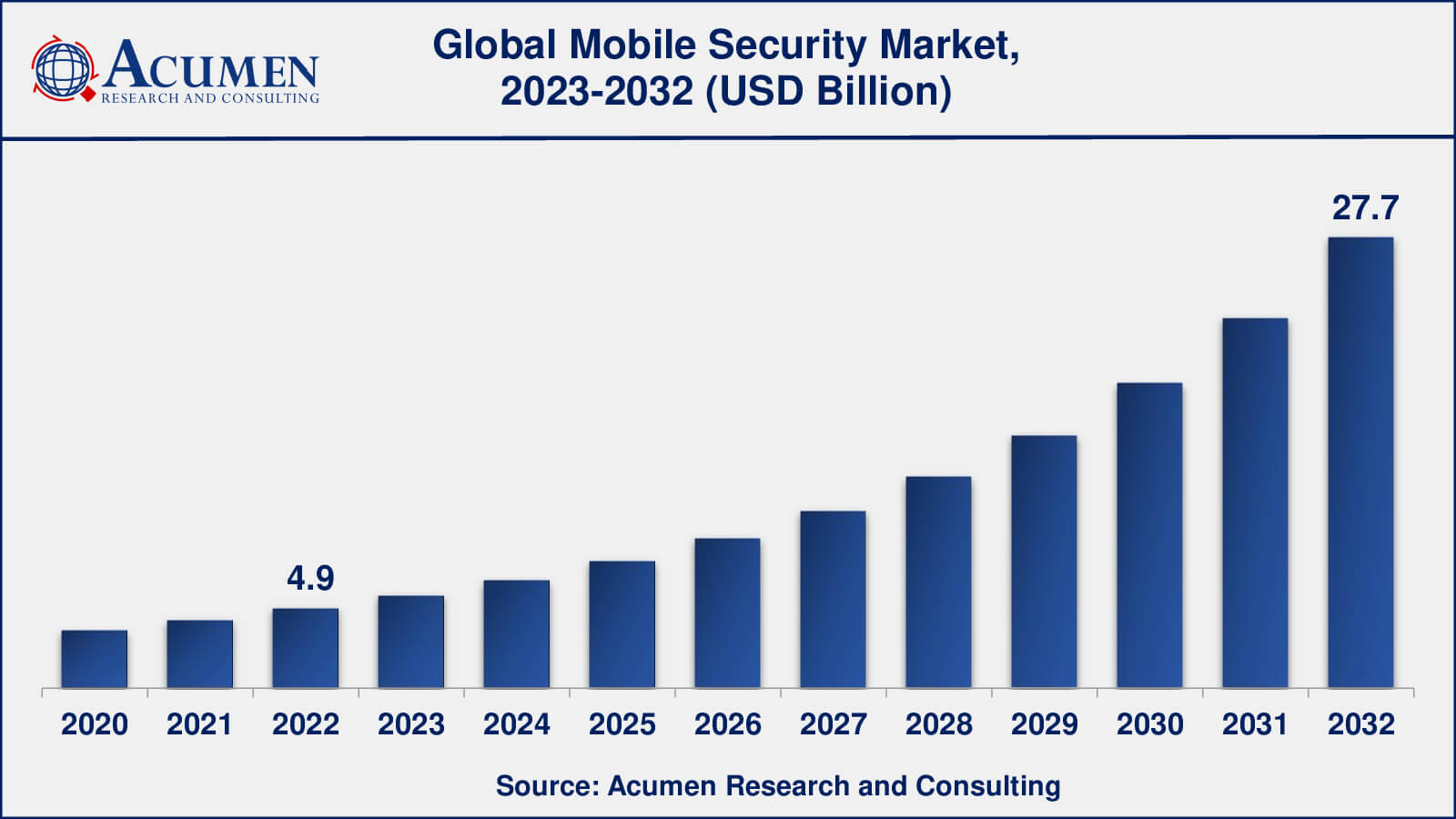
Mobile Security Market Size accounted for USD 4.9 Billion in 2022 and is estimated to achieve a market size of USD 27.7 Billion by 2032 growing at a CAGR of 17.1% from 2023 to 2032.
The Global Mobile Security Market Size accounted for USD 4.9 Billion in 2022 and is estimated to achieve a market size of USD 27.7 Billion by 2032 growing at a CAGR of 17.1% from 2023 to 2032.
Mobile Security Market Highlights

Mobile security is defined as the protection of smartphones, laptops, tablets, and networks from vulnerabilities and threats coming with wireless computing. The term mobile security is broad and covers everything from reducing risk and securing devices and their data in case of theft, shielding mobile devices from malware threats, to accidental loss or unauthorized access of the mobile device. Securing mobile devices has become very important in recent years owing to the fact that the number of devices and the uses to which they are put has expanded tremendously. The amount of sensitive information accessible by mobile devices has risen majorly in the past couple of years and there are no signs of it reducing. This data makes devices extremely valuable and a target for attackers. There are three main targets for threats: identity, information, and availability.
Global Mobile Security Market Dynamics
Market Drivers
Market Restraints
Market Opportunities
Mobile Security Market Report Coverage
| Market | Mobile Security Market |
| Mobile Security Market Size 2022 | USD 4.9 Billion |
| Mobile Security Market Forecast 2032 | USD 27.7 Billion |
| Mobile Security Market CAGR During 2023 - 2032 | 17.1% |
| Mobile Security Market Analysis Period | 2020 - 2032 |
| Mobile Security Market Base Year | 2022 |
| Mobile Security Market Forecast Data | 2023 - 2032 |
| Segments Covered | By Offering, By Operating System, By End-Use, By Industry Vertical, By Organization Size, And By Geography |
| Regional Scope | North America, Europe, Asia Pacific, Latin America, and Middle East & Africa |
| Key Companies Profiled | AVG, Kaspersky Lab, McAfee, Symantec, Apple, AegisLab, Avast, BullGuard, Bitdefender, CA Technologies, Fortinet, Cisco, F-Secure, Quick Heal, Juniper Networks, Sophos, and Trend Micro. |
| Report Coverage |
Market Trends, Drivers, Restraints, Competitive Analysis, Player Profiling, Covid-19 Analysis, Regulation Analysis |
Mobile Security Market Insights
Many small and medium businesses adopt BYOD (Bring Your Own Device) into their business environment; therefore the demand for mobile security is on the rise. Some of the major factors driving the mobile security market include mobile payments, protection of DRM (Digital Right Management), protection of VPN (Virtual Private Network), BYOD, and the need for a superior level of security to perform financial transactions. On the other hand, some of the restraining factors associated with mobile security include the high cost associated with the threat of hackers breaching the security channels, integrating solutions, accessing critical data, lack of awareness among consumers in certain regions, and complexity of embedded device security.

Mobile Security Market Segmentation
The worldwide market for mobile security is split based on offering, operating system, end-use, industry vertical, organization size, and geography.
Mobile Security Market By Offering
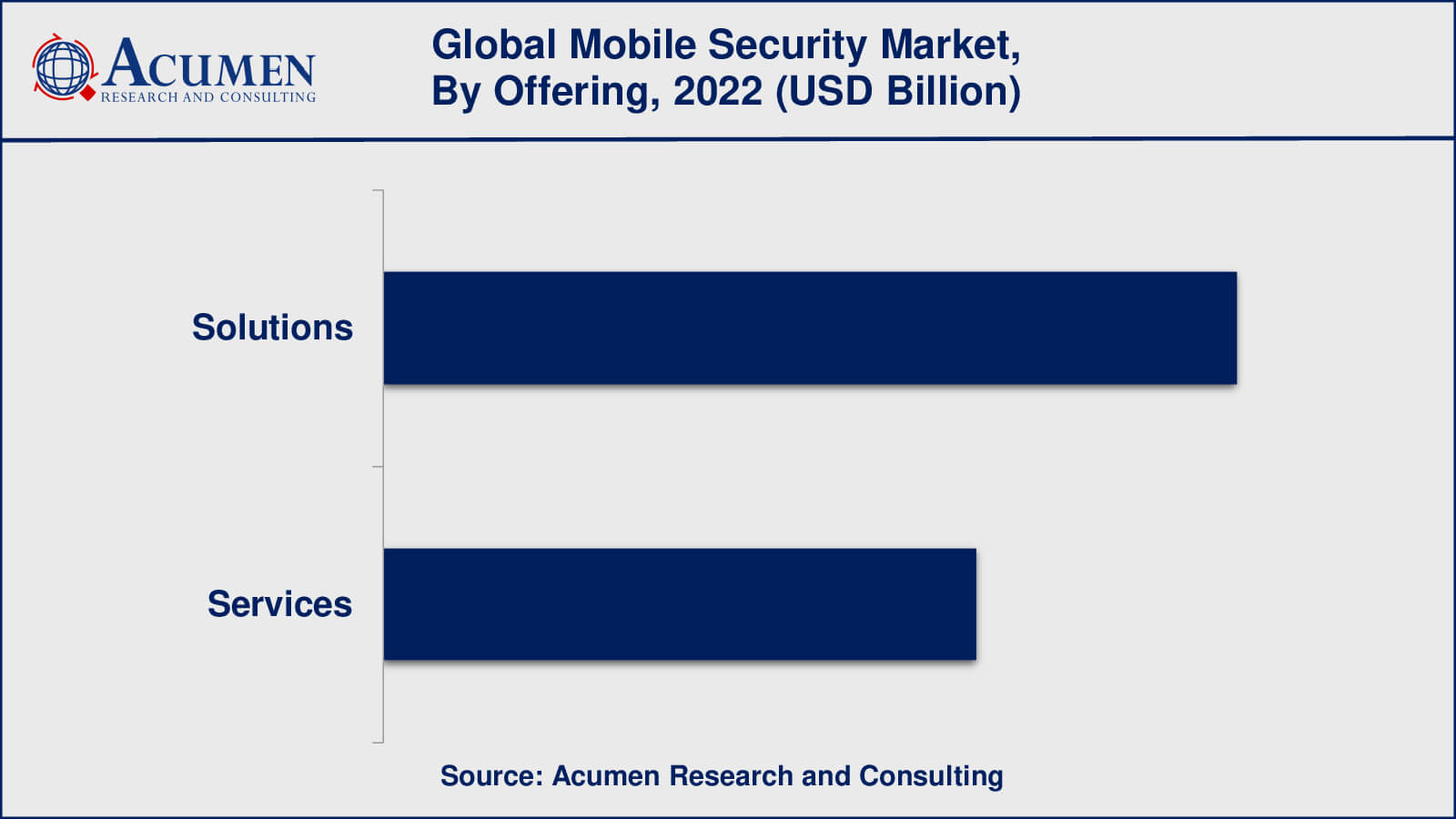
According to a mobile security industry analysis, the solutions segment includes mobile application security, mobile device security, identity and access management, mobile data protection, mobile device management, and mobile virtual private network (VPN) among others. These solutions are intended to protect mobile devices from a variety of threats such as malware, viruses, phishing attacks, and other cyber-attacks.
Furthermore, the solutions segment includes services such as consulting, integration and implementation, and managed services, which vendors provide to assist customers in implementing and managing mobile security solutions. The solutions segment's dominance can be attributed to the increasing adoption of mobile devices and the growing awareness of the importance of mobile security.
Mobile Security Market By Operating System
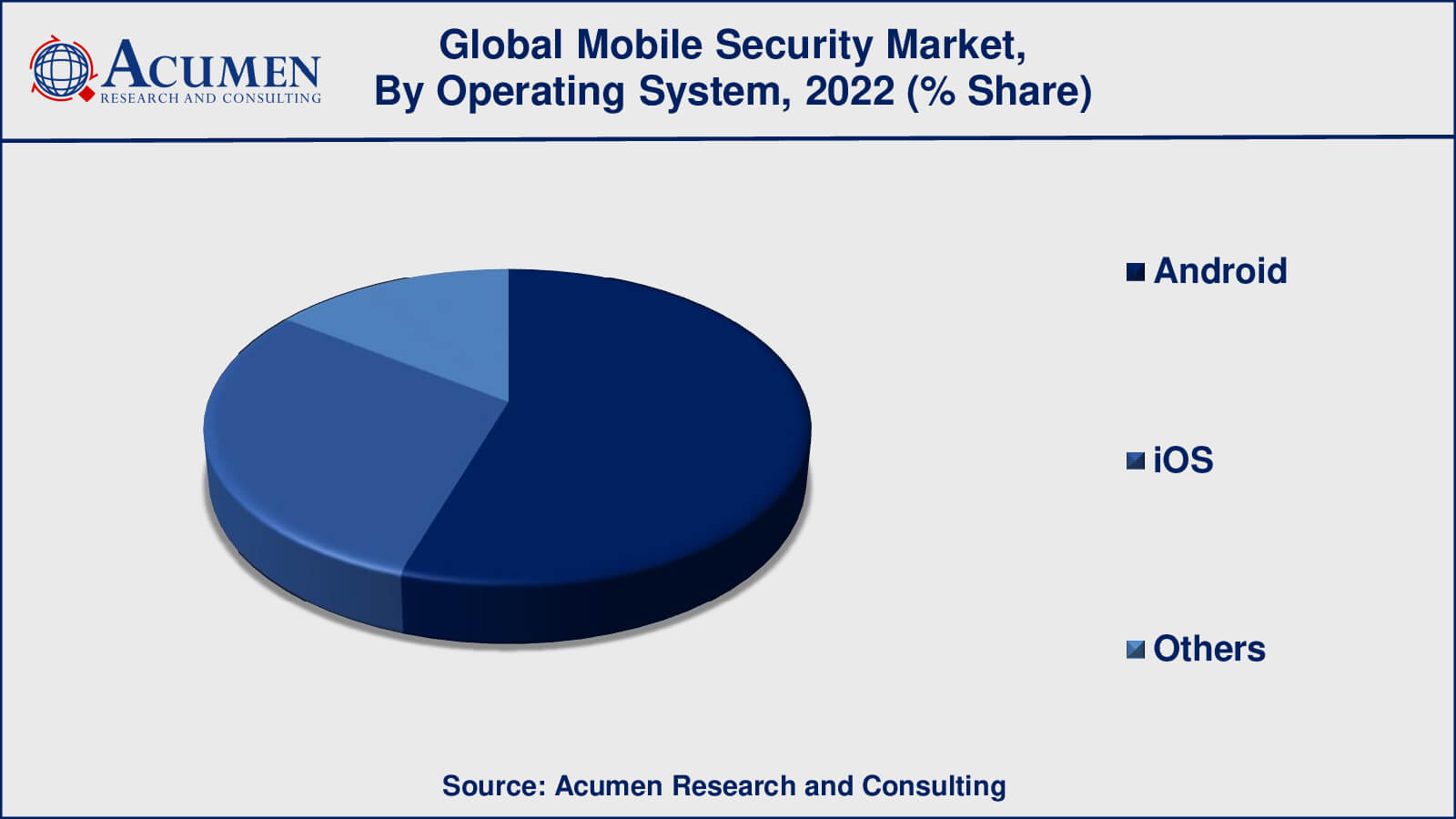
According to the mobile security market forecast, Android is expected to be the largest operating system in the mobile security market. Android is the most popular mobile operating system in the world, accounting for more than 70% of the market in 2021. As a result, it has become a primary target for cybercriminals looking to exploit vulnerabilities in the Android platform and compromise Android-powered mobile devices.
While iOS has grown in popularity in the mobile security market as a result of its reputation for strong security features, Android continues to dominate the market due to its widespread adoption and the fact that it is an open-source operating system that allows for greater flexibility and customization.
Mobile Security Market By End-Use
In recent years, enterprises have dominated the mobile security market. This is due to enterprises having a larger attack surface and being more vulnerable to security breaches than individuals. Enterprises typically use a greater number of mobile devices, which complicates managing and securing those devices. Furthermore, business data is frequently more valuable and sensitive than personal data, making it a more appealing target for cybercriminals.
While enterprises have dominated the mobile security market, the individual segment is becoming increasingly important. This is because mobile devices are increasingly being used for personal activities such as online banking, shopping, and social media. As a result, people are becoming more aware of the importance of mobile security solutions for protecting their personal information and privacy. Responding to this demand, vendors have created a variety of mobile security solutions aimed specifically at individual consumers, such as antivirus and anti-malware software, password managers, and VPN solutions.
Mobile Security Market By Industry Vertical
In recent years, the BFSI (Banking, Financial Services, and Insurance) industry has dominated the mobile security market. This is because the BFSI sector handles large amounts of sensitive and confidential data, making it an attractive target for cybercriminals. Employees in the BFSI sector are increasingly using mobile devices to access and manage this data, which has enhanced the demand for mobile security solutions.
While the financial services industry has dominated the mobile security market, other industry verticals such as telecom & IT, retail, healthcare, government & defence, manufacturing, and others are also adopting mobile security solutions to protect sensitive data and ensure compliance with security regulations.
Mobile Security Market By Organization Size
In recent years, large enterprises have dominated the mobile security market. This is because large enterprises have a larger attack surface and are more susceptible to security breaches than small and medium-sized businesses (SMEs). Large enterprises frequently use a large number of mobile devices, which complicates managing and securing those devices.
While large enterprises have controlled the mobile security market, the SME segment is becoming increasingly important. This is due to the increasing use of mobile devices for business activities By Organization Size, as well as the need for these businesses to protect sensitive data. Responding to this demand, vendors have created a variety of mobile security solutions aimed specifically at SMEs, such as antivirus and anti-malware software, password managers, and VPN solutions.
Mobile Security Market Regional Outlook
North America
Europe
Asia-Pacific
Latin America
The Middle East & Africa
Mobile Security Market Regional Analysis
North America is one of the largest markets for mobile security solutions, driven by the high adoption of mobile devices and the increasing frequency of cyber-attacks. The United States is the region's largest market, accounting for a sizable portion of the global market.
Europe is another important market for mobile security solutions, driven by rising awareness of the importance of mobile security and the expansion of the mobile workforce. The region's major markets are Germany, France, and the United Kingdom.
Asia-Pacific is the fastest-growing market for mobile security solutions, owing to rising mobile device adoption and the expansion of the mobile workforce. The region's major markets are China, India, and Japan.
Mobile Security Market Players
The global mobile security market is analyzed to witness high competition among the players as the market is still in its promising stage. The manufacturers are making huge investments in R&D to meet the growing requirement for advanced mobile security solutions. The demand in emerging economies is especially high because they have large numbers of customers demanding mobile security solutions. Companies in the market primarily compete on compatibility issues in order to retain the market share.
Some of the top mobile security companies offered in the professional report include AVG, Kaspersky Lab, McAfee, Symantec, Apple, AegisLab, Avast, BullGuard, Bitdefender, CA Technologies, Fortinet, Cisco, F-Secure, Quick Heal, Juniper Networks, Sophos, and Trend Micro.
Looking for discounts, bulk pricing, or custom solutions? Contact us today at sales@acumenresearchandconsulting.com
March 2023
April 2025
April 2025
March 2025